IoT Security Sessions - ESC San Jose 2021

San Jose 2021 DriveWorld & Embedded Systems Conference
Joe Hopper, a Principal Security Consultant at Fracture Labs, shares his expertise in IoT security at the 2021 DriveWorld & Embedded Systems Conference in San Jose on August 18, 2021. In his two sessions, he will be demonstrating live hacks against off the shelf IoT devices and will walk through how hackers approach embedded systems.
Live Hack: Exposing Common IoT Security Weaknesses
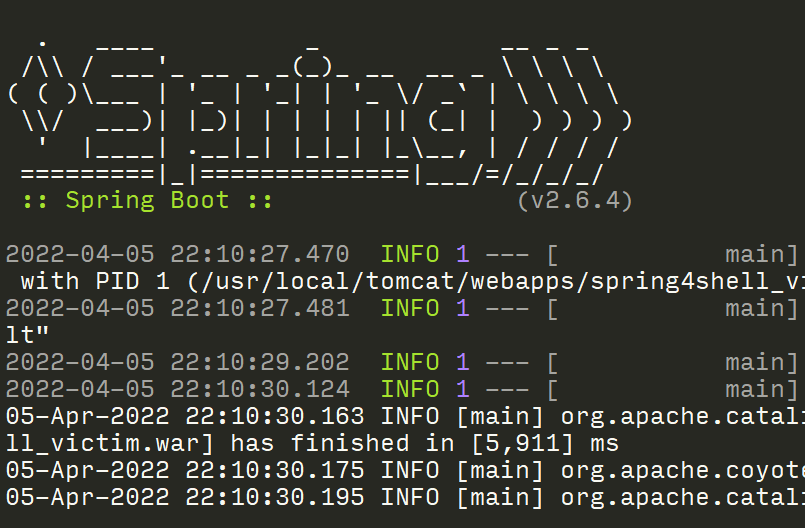
Have your embedded systems been built with appropriate security controls in mind? Joe Hopper, Principal Security Consultant at Fracture Labs, will demonstrate several complex hacks against off-the-shelf IoT devices to shed light on the design and implementation weaknesses seen across the industry. He will walk through common attacks such as: finding and connecting to hidden serial consoles, boot process hijacking, memory analysis, firmware extraction, password cracking, and more to gain unauthorized access to IoT devices and customer information.
By using the same approach hackers use against your devices, you will walk away with a better understanding of where and how you need to tighten security controls.
Internet of Insecure Things: Through the Eyes of a Hacker
Hackers don’t see “just a smart light” or “only a telematics sensor.” They see a computer that allows them to steal intellectual property, grab sensitive data, cause physical damage and injuries, or pivot into a victim’s network!
As a professional hacker, Joe Hopper of Fracture Labs will take you through the mindset of a hacker. You’ll learn what motivates hackers, how they approach an attack against your IoT systems, and what stops them. By the end, you will understand common attacks against hardware, software, and communication signals so you can incorporate tighter security controls in your products.
The team at Fracture Labs has hacked a myriad of systems, including defense vehicles, aircraft, municipal smart lighting, medical devices, and many others! Let their experience with embedded system security give you a head start on securing your devices from chip to cloud!
Key Takeaways:
- Who the attackers target and why
- Overview of the types of threats facing IoT systems
- Tips to harden your IoT system against hackers
What’s Next?
Please reach out if you’d like more information regarding our smart device security assessments!
Let us know what you think
Please share this post if you found it useful and reach out if you have any feedback or questions!
Big Breaks Come From Small Fractures.
You might not know how at-risk your security posture is until somebody breaks in . . . and the consequences of a break in could be big. Don't let small fractures in your security protocols lead to a breach. We'll act like a hacker and confirm where you're most vulnerable. As your adversarial allies, we'll work with you to proactively protect your assets. Schedule a consultation with our Principal Security Consultant to discuss your project goals today.