-
DEEP608 Conference - IoT: The 'S' Stands for Security
Fracture Labs presents at DEEP608 regarding the risks IoT devices pose to organizations and what can be done to reduce the risk.
-
RF Replay Attacks: Hacking Christmas Tree Lights
Fracture Labs uses Christmas tree lights as an example of how easy it is to hack poorly implemented RF communication found in many IoT devices.
-
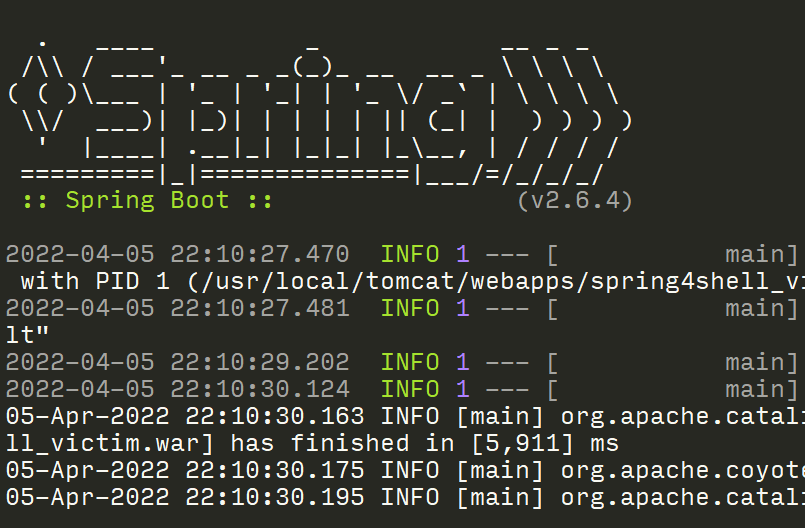
Effective Spring4Shell Scanning and Safe Exploitation
Scanning for and exploiting the Spring4Shell vulnerability can be tricky, but this post will show you how to scan more effectively using custom tools from Fracture Labs
Big Breaks Come From Small Fractures.
You might not know how at-risk your security posture is until somebody breaks in . . . and the consequences of a break in could be big. Don't let small fractures in your security protocols lead to a breach. We'll act like a hacker and confirm where you're most vulnerable. As your adversarial allies, we'll work with you to proactively protect your assets. Schedule a consultation with our Principal Security Consultant to discuss your project goals today.