Security Camera Hacking
This post was inspired by some work we did almost two years ago, but never got around to fully documenting or reporting the issues to the vendor since this was just independent research. We wanted to have all of the attacks fully baked before reporting the issues, but then moved on to other projects. So I’ve decided to go back and redo all of the work on this to properly document everything. I will be blurring out any identifying information until the vendor has had a chance to respond, so for now I’ll just refer to the vendor as ‘CompanyX’.
So to bring us back to the start, we bought a midrange security camera around the end of 2014 performed a security deep-dive on it. We found some troubling issues including command injection and buffer overflow vulnerabilities, and more troubling, the means to call out to Chinese IP space for what appears to be remote control and patching capabilities.
The ultimate goal of the project is to determine if an unauthenticated, remote hacker could obtain complete control of the device. To do this, we broke the plan of action down into a few distinct phases:
Dynamic Analysis
What vulnerabilities could we discover through the UI or other network-based services?
Static Analysis (coming soon)
What could we learn from the vendor-supplied firmware, or any other files we may be able to pull off of the device’s on-board storage?
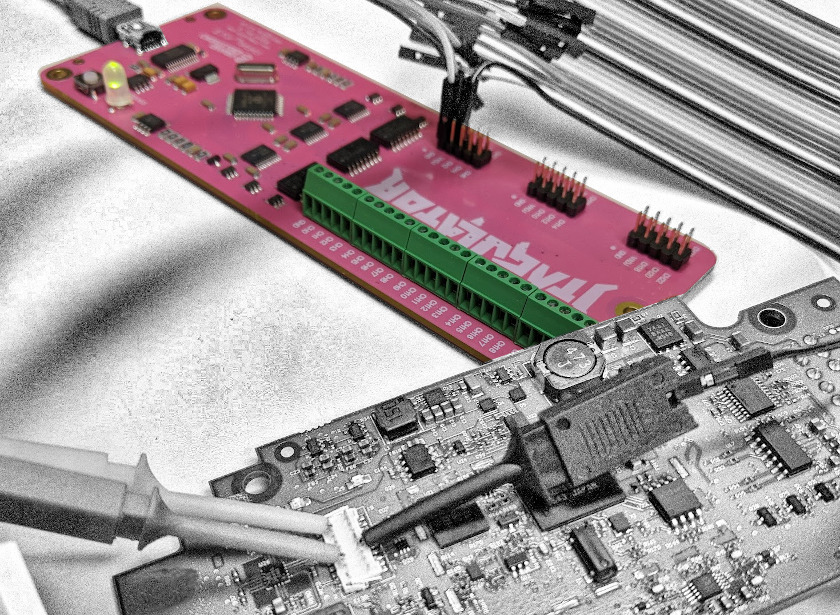
Physical Analysis (coming soon)
Can we pull the firmware off the device directly? Are there any debugging ports available for us?
Exploitation! (coming soon)
What could we do with the device given the vulnerabilities we discovered?
Let us know what you think
Please share this post if you found it useful and reach out if you have any feedback or questions!
Big Breaks Come From Small Fractures.
You might not know how at-risk your security posture is until somebody breaks in . . . and the consequences of a break in could be big. Don't let small fractures in your security protocols lead to a breach. We'll act like a hacker and confirm where you're most vulnerable. As your adversarial allies, we'll work with you to proactively protect your assets. Schedule a consultation with our Principal Security Consultant to discuss your project goals today.